Cyber Security
Recently, cyber security has emerged as a corporate management risk with the acceleration of the digital transformation. In addressing these concerns, Hyundai Steel has acknowledged the importance of cyber security and has tasked the Audit Committee, under the BOD, to oversee Security risks(personal information, cyber security, etc.), as well as acquiring the ISO 27001 standard. We are also strengthening the management of security system operations and boosting in-house security training.
Security Policy Implementation and Diagnosis
Hyundai Steel has security policies that are implemented and diagnosed for the safe management of corporate security. The principal goal of our security policy is the 'protection of tangible and intangible business information and technical information'. Through our in-house standards management system, we disclose our 'Regulations on Security Management', which include rules on entry, everyday security rules, personal information protection, and rules for suppliers/outsourcing companies, in order to guide employees on how to respond immediately in case of emergency. We diagnose security policies through the Hyundai Motor Group's security level assessment, and through the ISO 270001 certification audit conducted annually. In addition, we use hacking simulations to enhance our security level for us diagnose our IT system and infrastructure every year, and set out measures to mitigate exposed vulnerabilities. We introduced company-wide security performance evaluation(KPIs) to enhance employees' understanding of security policies and compliance. Based on the security management regulations, 41 items for point deduction and 16 items for point addition(57 items in total) are evaluated on a quarterly basis, evaluation results are notified and improvement activities are carried out.
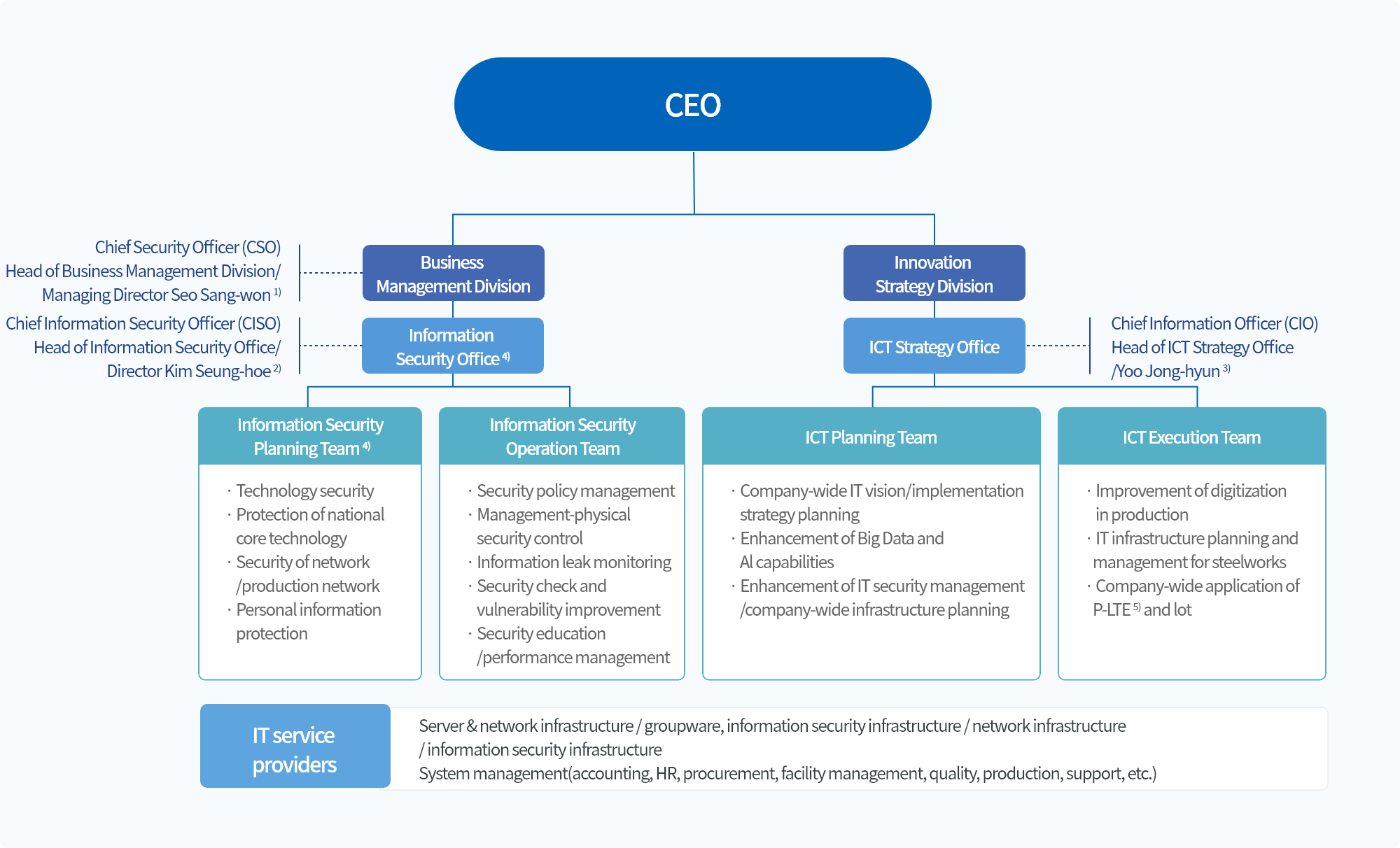
- 1) Decision making on information security
- 2) 27 years of experience in information protection and technology, chief information protection officer of Hyundai Steel(final approval of establishment and operation of security regulations and policies, responsible for company-wide security management, and authority to supervise security inspection/order audits)
- 3) Chief officer for information system and resources management
- 4) Information Security Office and Information Security Planning Team established(January 1, 2022)
- 5) P-LTE(Private LTE): intelligent network control technology
Security Education
Hyundai Steel holds semi-annual security meetings for all employees, which is composed of security issues and trends, basic security information, policy guidance, personal information protection, and trade secret protection. To enhance employees' understanding, we produce and utilize educational videos on such topics as ransomware prevention and information leakage threats. In the first half of 2022, online training on cyber threats and trade secret protection was conducted for all employees, and customized security training was provided to heads of departments/teams. All training courses were conducted in a non-face-to-face/online format considering circumstances around the COVID-19 pandemic. We also provided a range of education courses to newly promoted employees, newly hired employees, expatriates, and employees who failed on mock phishing drills. In addition to the existing training methods, various new channels such as SNS/mobile environment are adopted or under consideration, in order to make our education courses timelier and more accessible. We conduct satisfaction surveys on education courses, and make improvements accordingly to promote effectiveness.
Protection System for National Core Technologies
In accordance with the revised Industrial Technology Drain Prevention Act, Hyundai Steel has strengthened its security management system for the national core technologies1) it owns. In particular, we have established a national core technology protection organization, which defines, identifies and manages core technologies, and added 12 special security areas to enable more stringent security control. We revise security management regulations and rules, collect security pledges, provide security education, conduct self-inspection and check on the management status of national core technologies. Through field-oriented, practical protection of core technologies, the Company will continue to comply with relevant laws and regulations.
- 1) Current status of National Core Technologies owned by Hyundai Steel
- ① Rebar/section steel manufacturing technology with a yield strength of 600MPa or higher
- ② Giga-class, high-strength steel sheet manufacturing technology with a sum of total alloying elements of less than 4%
Training and Reporting System to Prevent Cyberattacks
Hyundai Steel has expanded phishing simulation for all employees, increasing their frequency from semi-annual to quarterly drills since 2021. Training contents reflect various social engineering attacks and types(e.g. induce users to click links, phishing sites, or attachment of malignant files) with the view of reinforcing security awareness against cyberattacks. The Company newly introduced a simulated phishing training system in the first quarter of 2022 by utilizing multiple training contents instead of one. Based on the analysis and results, employees who are vulnerable to phishing are provided with additional, in-depth training. Starting 2022, we plan to conduct additional simulated drills more than three times for employees who repeatedly fall for phishing, to raise employees' awareness to prevent and deal with damage.
Moreover, Hyundai Steels established a reporting system to prevent cyber-attacks. If there is any case suspected of a cyberattack or damage is incurred, our employees report it to our security organization and security control department in no time. Upon receipt of a report, security managers take prompt measures to recover from damage and take follow-up actions, such as blocking the attack route, and backing up data and initializing computers of infected employees. Through continuous training, we will promptly respond to cyberattacks, take countermeasures, and maintain stability.
Suggestion and Reporting System for Security Control
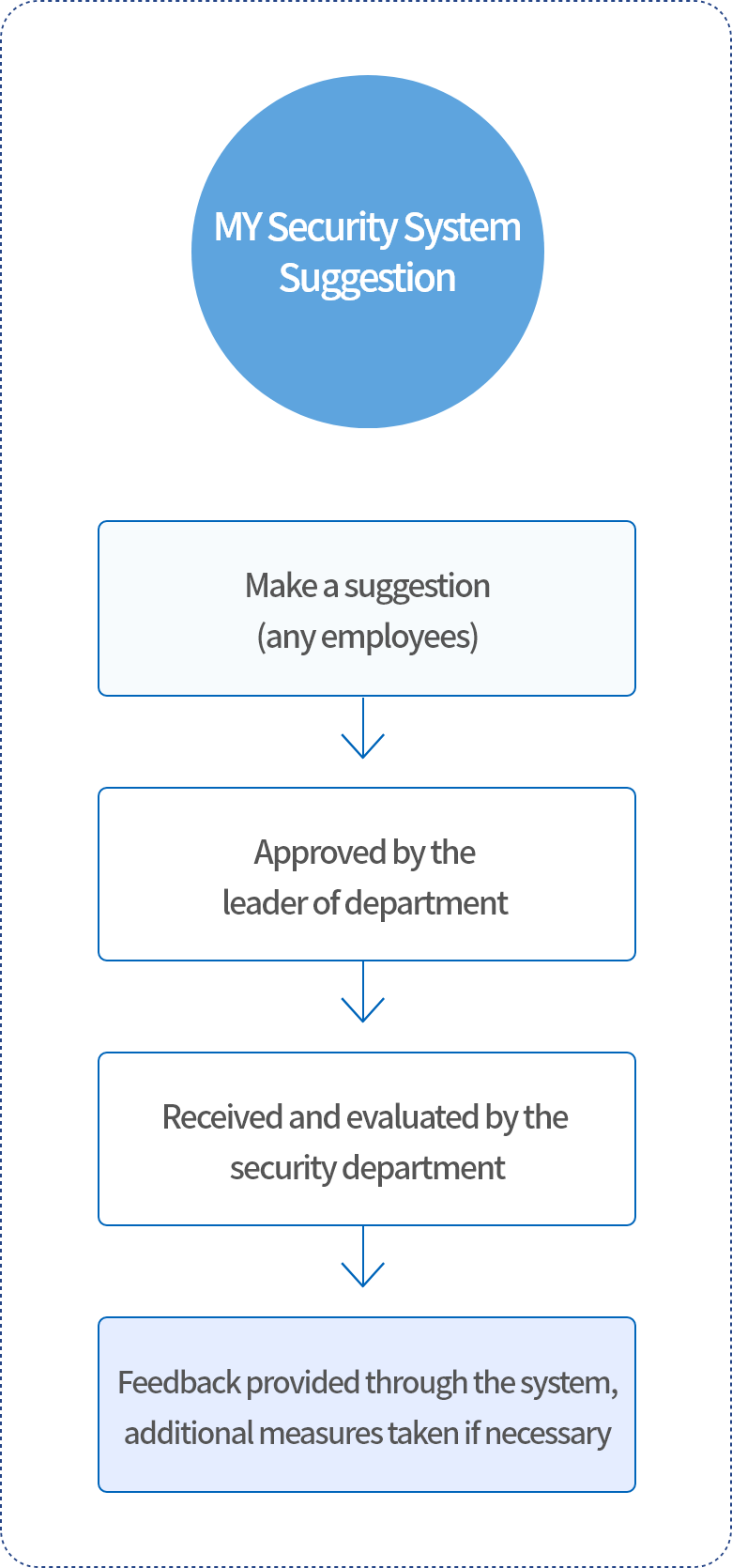
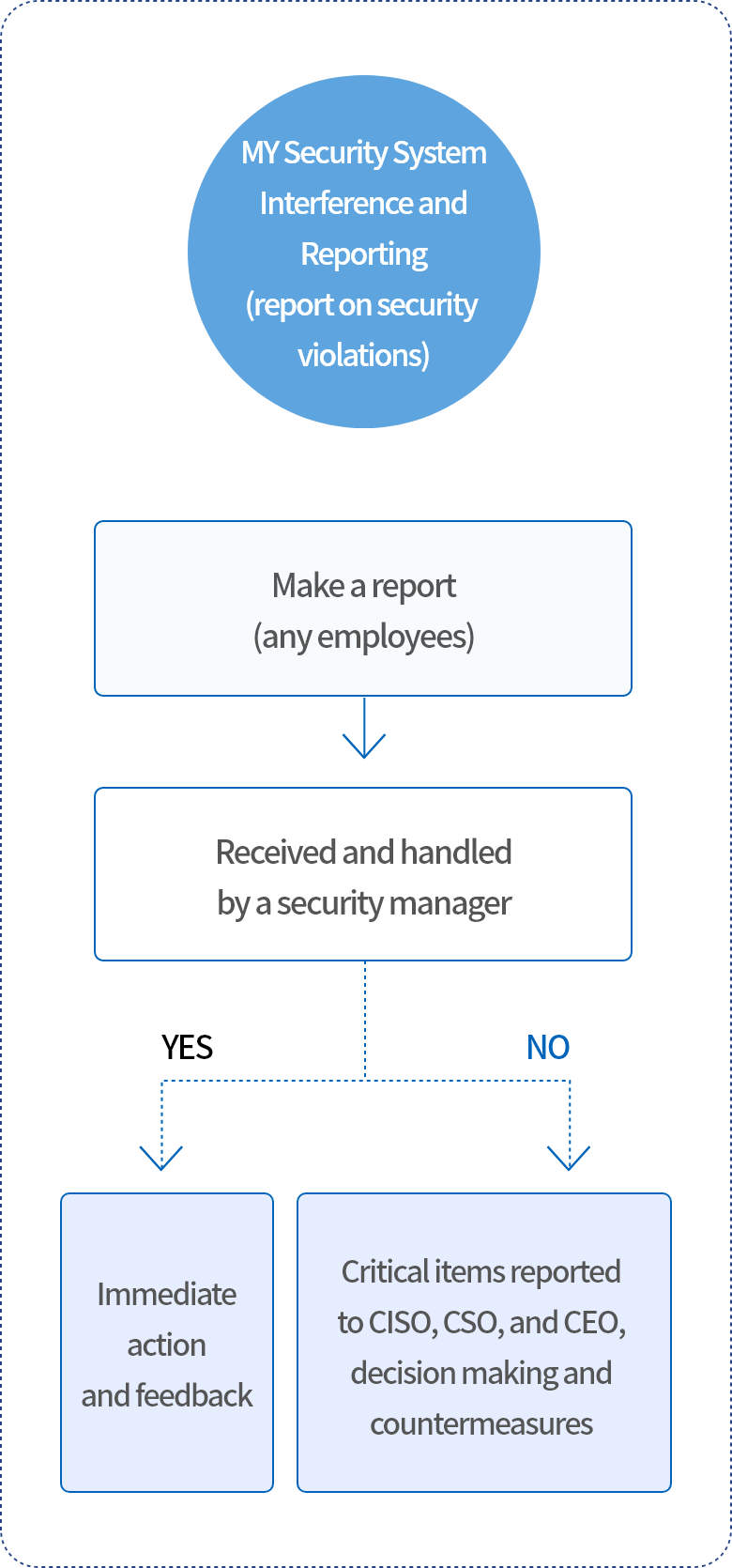
Hyundai Steel operates a system where our employees can make suggestions, report threats or problems relating to information protection, and express opinions. Items of high priority are reported to the top management, and actions are taken for improvement. Besides, various security channels can be used for sharing security threats, just as the aforementioned suggestion and reporting system. Through these multiple channels of communication, we promptly deal with security violations, threats, etc., take actions and provide feedback.
MY Security System Suggestion
MY Security System interference and Reporting(report on security violations)
Security Authentication
ISO 27001(Information Security Management System) Certification
Hyundai Steel continues to diagnose its security systems and take improvement measures through assessment as part of international security standard certification. In the second half of 2020, we received assessment for the ISO 27001 certification which is conducted every three years and was recertified after document review and on-site inspection in 14 sectors of certification standards. We received additional assessment in the first/second half of 2021, the first half of 2022 and maintained the certification. Even in the future, Hyundai Steel will maintain international security standard certifications and strengthen its excellence in security.
IT Infrastructure and Information Security Management System Verification
Hyundai Steel conducts self-inspection and verification of its information security system(IT infrastructure and information security management system) in order to check and improve its safety. We also receive external verification by ISO 27001 certification and continuously receive from infrastructure inspection a specialized external agency for the purpose of diagnosing and removing weakness. Highly sophisticated hacking simulation is conducted by Ahnlab experts and a specialized agency assesses the security setting and management status of our infrastructure(OS, DBMS, WEB/WAS). As such, we strive to reinforce the security of IT infrastructure and system, and maintain their stable operation through continuous security control.